One of the most prevalent security incidents in smaller enterprise environments is the installation of Potentially Unwanted Programs (PUPs). Allowing every employee to install software at their discretion is likely to lead to unwanted or malicious programs infiltrating the company's environment. A core principle of modern zero-trust security is not trusting any user or program by default. All software deployed in the environment needs to be vetted carefully before installation.
Group Policy can be used to lock down systems so users cannot install any software without administrator elevation. Another feature that can take this a step further is Application Whitelisting. This control prevents all software from running by default. Admins have to go in and manually whitelist the programs that are approved for the environment. Application whitelisting forces software to run on a need-to-know basis. Employees can only run the bare minimum software to do their work.
Different device management platforms have their own strategies for implementing app whitelisting. Microsoft InTune and Apple Configurator are two Mobile Device Management platforms that allow an admin to set app whitelisting policies for devices. Depending on the devices running, InTune may be the preferred option for smaller organizations, as it supports management for Windows, macOS, iOS, and Android devices.
The basic implementation of application whitelisting is done with the Windows AppLocker feature. If your network runs a handful of Windows PCs on a domain or workgroup network, then AppLocker should suffice for configuring application whitelisting.
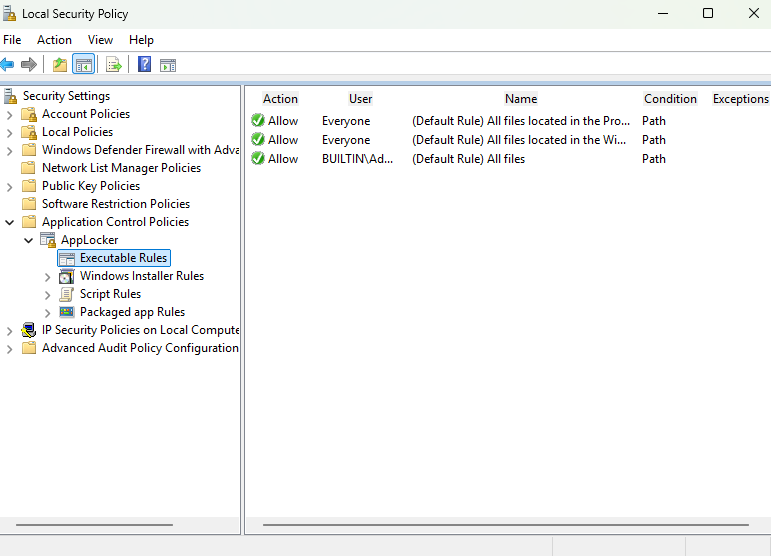
AppLocker is configured through the Windows Local Security Policy on workgroup networks and Group Policy Management console on domain networks:
AppLocker allows you to whitelist applications through three rule conditions:
- File Publisher
- File Path
- File Hash
For demonstration, I am going to restrict my Office Staff group to using only the necessary programs for their daily workflows. I start by generating Default Rules in AppLocker. These are the templates that will be used to create more granular rules.
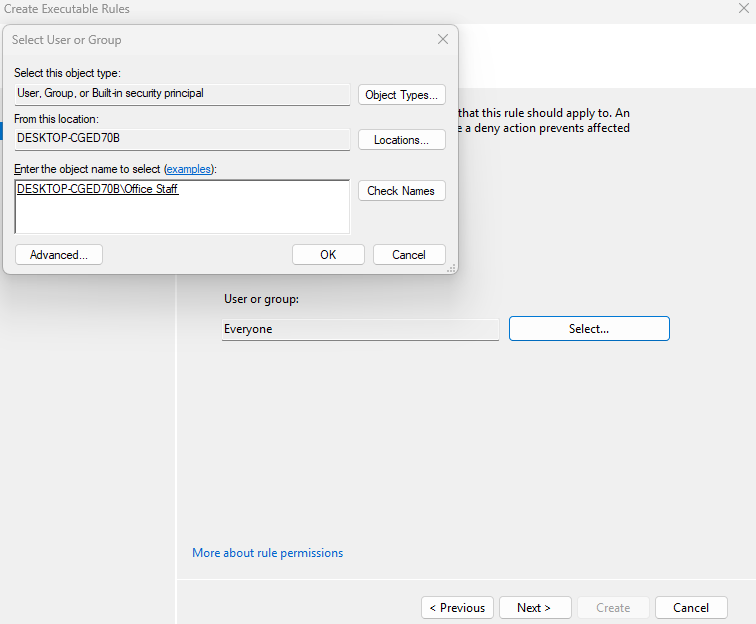
I can then begin creating a new AppLocker rule for my Office Staff local user group.
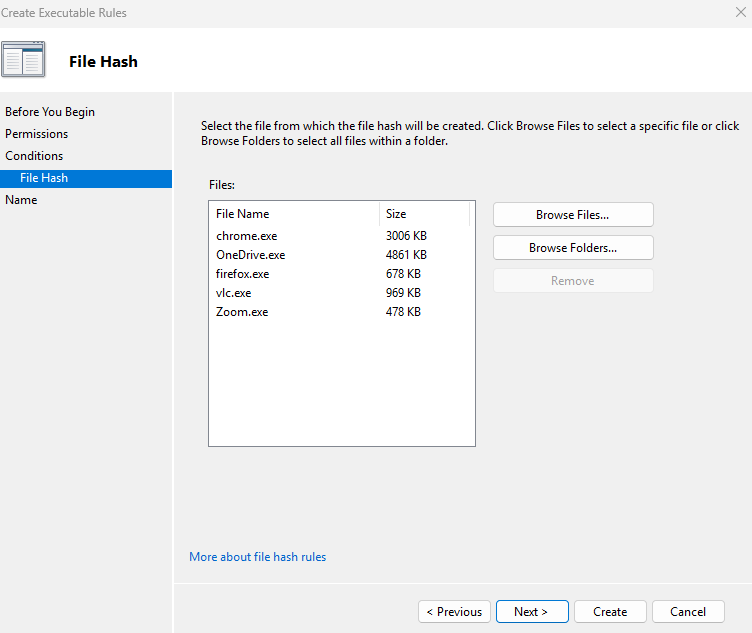
For this demo, I want to allow Chrome, OneDrive, Firefox, VLC, and Zoom.
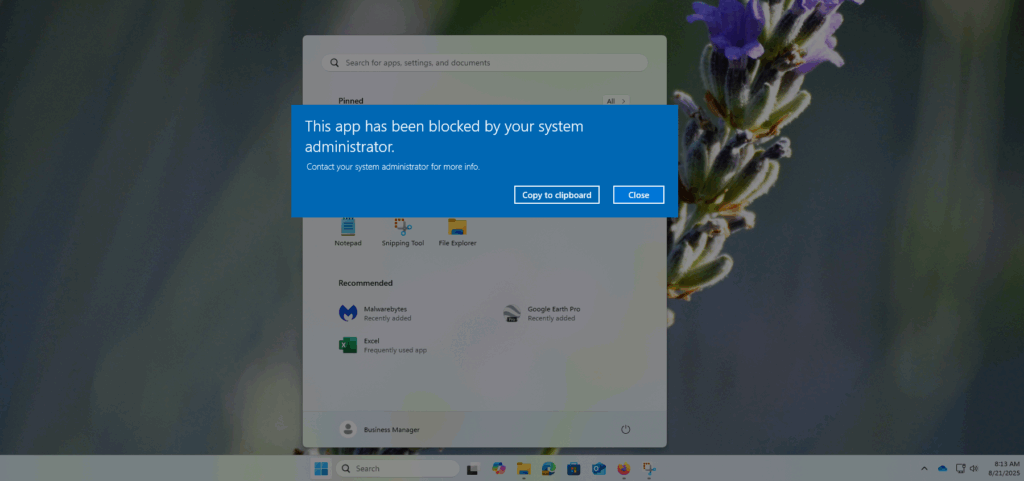
Once the rule is created, all office users will be permitted to access only the above-specified programs. Attempting to access a different program will result in an error from Windows.
Application Whitelisting is an extremely powerful way to limit the attack surface of your systems. Combining it with strict access controls will limit the possibility of your employees bringing in unwanted or malicious applications to your environment.
