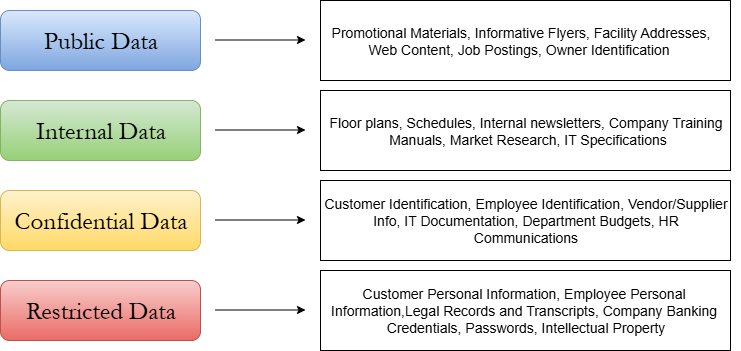
Now that you have a holistic view of your organization’s data, you can move into classifying it and assigning ownership. A major security vulnerability present in SMB environments is a complete lack of governance and ownership of their data. If you cannot manage your data lifecycle and assign accountability, you will inevitably lose track of how your data is processed, stored, and transmitted, and before you know it, a sensitive HR document has been leaked onto social media. Two main data classification schemes are used. The most common and recommended scheme is the Corporate model, which uses four classification levels:
- Public: This data is produced for use in public spaces and will not affect company security if shared. Think event advertisements, job listings, and social media notifications.
- Internal: This data is produced for internal company use only. However, if it does happen to be publicly disclosed, it will not cause any serious damage to your organization. Think product pricing plans and project roadmaps.
- Classified: This data is meant for internal usage only and could result in serious damage to your organization if disclosed. Think trade secrets and business communications with other organizations.
- Restricted: This is the most sensitive category of data that can cause extreme damage if disclosed. This data needs to be protected with defense-in-depth controls like encryption and strict access controls. This category usually includes Personally Identifiable Information (PII) and Protected Health Information (PHI).
The second major data classification scheme is the US National Security Classification scheme:
- Unclassified: Information that has not otherwise received a sensitivity label and is generally subject to disclosure under the Freedom of Information Act (FOIA). Unclassified doesn’t necessarily mean harmless, just that it hasn’t been classified yet. Information in this category may be selected for exemption from FOIA requests by labelling it Controlled Unclassified Information (CUI).
- Confidential: Information that, if disclosed, could reasonably be expected to damage national security posture.
- Secret: Information that, if disclosed, could reasonably be expected to seriously damage national security posture.
- Top Secret: Information that, if disclosed, could reasonably be expected to cause exceptionally grave damage to national security posture.
The corporate classification scheme makes the most sense to use in an SMB environment. However, if you find the US National Security Classification scheme makes more sense, nothing is stopping you from using it in a business scenario. Regardless of which scheme you choose, make sure every data type uncovered in the previous section is thoroughly reviewed and assigned a classification label.
Examples of Personally Identifiable Information (PII):
- Name (full name, maiden name, mother's maiden name, alias)
- Social Security Number (SSN)
- Passport Number
- Driver's License Number
- Taxpayer Identification Number
- Financial Account Number
- Credit Card Number
- Address Information (Street Address or Email Address)
- Photographic Image
- Fingerprints
- Handwriting
- Retina Scan
- Voice Signature
- Facial Geometry
- Information about an individual that is linked or linkable to one of the above(Date of birth, place of birth, race, religion, weight, activities, geographic indicators, employment info, medical info, educational info, financial info).
Examples of Protected Health Information (PHI):
- Any information concerning health status that can be linked to an individual
- Any information concerning healthcare that can be linked to an individual
- Any information concerning payment for health care payments that can be linked to an individual
