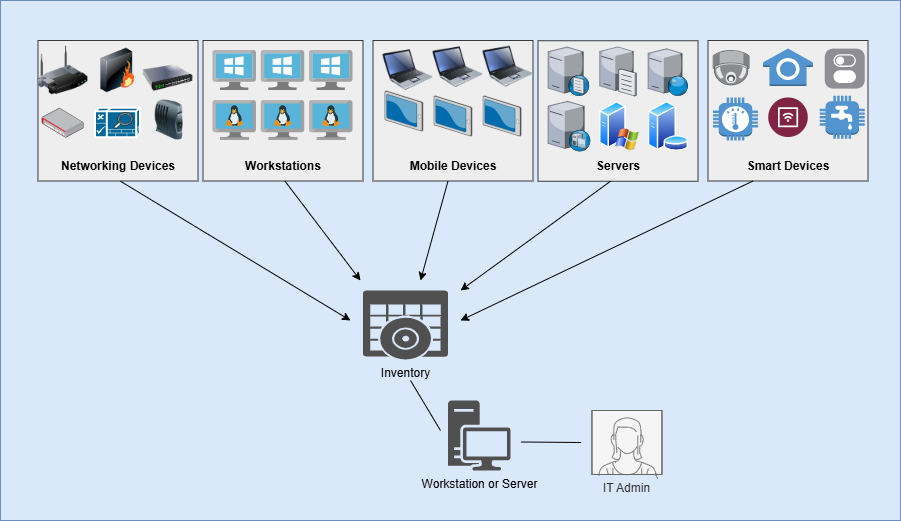
Businesses of all sizes usually implement many systems and devices in their network environments. Each one works together to provide a baseline level of network functionality daily. Examples of physical devices common in business environments include desktop computers, laptops, monitors, peripherals, printers, scanners, security cameras, routers, switches, access points, phones, tablets, and IoT smart devices. Each physical device utilized in a business environment has an inherent value to the business. Each device works in a larger system that enables the business to meet its goals and objectives. Properly securing these devices is essential for reducing the attack surface of the business and reducing risk to an acceptable level. The process of securing these devices starts with a thorough hardware asset inventory that will be maintained and updated on an ongoing basis. The hardware asset inventory documents all of the physical devices utilized in the business, along with important identifying information about them and their components. Each piece of hardware should be entered in the inventory with the following attributes specified:
- Asset ID
- Date of Purchase
- Purchase Price
- Asset Description
- Manufacturer
- Model
- Serial Number
- Asset Owner
- Assigned User(s)
- Hostname
- Business Department
- Physical Location
- MAC Address(es)
- IP Address(es)
- Warranty Expiration Date
- Licensing Info (if applicable)
- Connected Network
- Disposal Date
- Disposal Method
- Additional Notes