Network environments SHALL be macrosegmented using VLANs, with priority given to segregating IoT devices and systems with varying risk and impact levels from each other.
Control Type: Technical
Control Function: Preventive
Description: Even small business networks handle thousands of sessions and transactions daily. Network traffic generally flows in two directions: North-South and East-West.
North-South traffic refers to traffic that enters or leaves the local business network from the Internet. When employees log into websites, query DNS servers, or download files, they are generating North-South communication.
East-West traffic, on the other hand, occurs between hosts within the local network itself. When employees access local file servers, print to network printers, or log into an internal web portal, the traffic flows laterally within the network—hence, east-to-west.
Because so much traffic occurs on local networks, it is necessary to segment the network to better supervise and manage activity. A single, large network segment with hundreds of nodes moving laterally can become overwhelming and increase the network’s attack surface. Macrosegmentation, or simply network segmentation, is the process of dividing network nodes into smaller segments to reduce the attack surface. This not only improves network security but also makes the network more manageable.
Classic macrosegmentation is generally implemented using Virtual Local Area Networks (VLANs). VLANs allow network nodes to be grouped logically, regardless of their physical location within a facility, by assigning similar nodes to the same broadcast domain. A broadcast domain is a network segment where all devices can receive the same message. Each port on a standard switch is normally its own broadcast domain, but VLANs can group multiple ports into a single broadcast domain. Devices within the same VLAN can communicate with each other but are isolated from devices in other VLANs unless routing rules are configured.
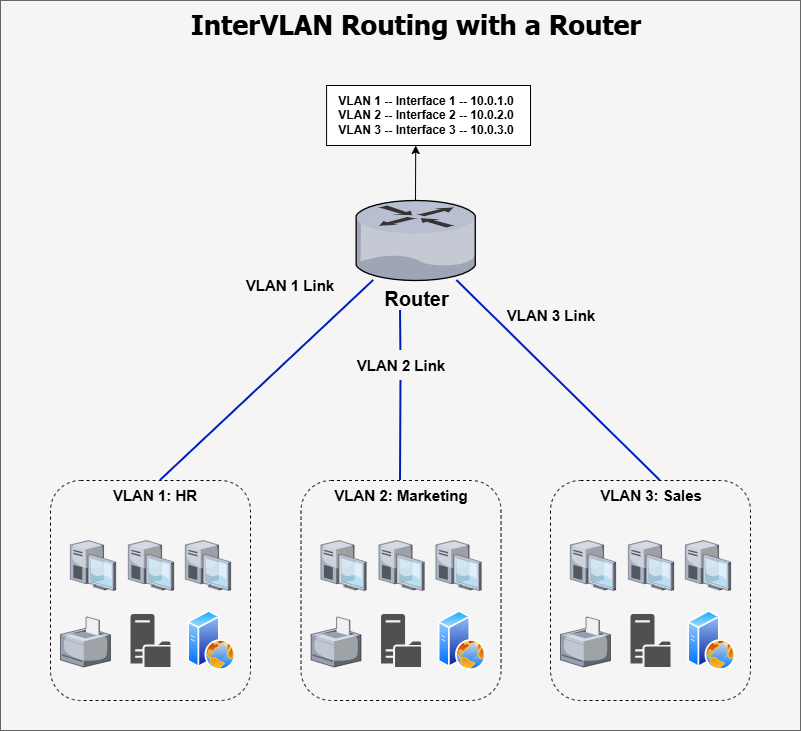
Practically, VLANs are used to group similar devices together. For example, an HR VLAN could contain all HR devices and servers, while a Marketing VLAN contains all Marketing devices and servers. Devices within each VLAN can communicate with others in their domain, but cannot directly reach devices in another VLAN. The name Virtual LAN makes sense because VLANs create small, logical networks within a larger physical network.

This approach greatly improves network security, but it reaches a limitation when devices in different VLANs need to communicate with each other or access the Internet. For traffic to flow between VLANs, Inter-VLAN routing must be configured. Because routing occurs at Layer 3 of the OSI Model, a Layer 3-capable device is required to handle traffic between VLANs. The two standard options are a router or a Layer 3 switch.
- Router: Each VLAN is connected to the router via a separate link. The router identifies the VLANs and directs traffic between them accordingly.
- Layer 3 switch: Each VLAN is assigned a Switch Virtual Interface (SVI). The SVI acts as the VLAN’s default gateway, and the switch routes any traffic destined for that VLAN through its SVI interface.

To control the flow of network packets, Access Control Lists (ACLs) can be applied. ACLs allow traffic to be permitted or denied based on source and destination IP addresses, as well as ports. They can be configured very granularly to meet the security requirements of each VLAN. For example, a VLAN hosting internal web applications could have an ACL that restricts access to only employee network segments, permitting communication solely on port 443 (HTTPS).
VLANs can be complex to configure for those without networking experience. Organizations need appropriate technology and expertise before attempting implementation. VLANs require managed switches, as unmanaged “plug-and-play” switches do not support segmentation. Routers and Layer 3 switches must also have sufficient capacity to handle Inter-VLAN traffic without degrading performance. Many businesses choose to outsource VLAN configuration to third-party IT providers to ensure proper implementation.
Regardless of how VLANs are deployed, they represent a critical network security control that all organizations should implement. Segmentation is particularly important with the proliferation of Internet of Things (IoT) devices, which are often insecure and can serve as easy entry points for attackers. If IoT devices share the same network segment as sensitive resources, adversaries can move laterally from compromised devices to critical systems. Any business with IoT devices should segregate them onto a separate network segment.
Different classes of employee devices also carry varying levels of risk. For instance, HR devices typically access sensitive personal data, whereas administrative assistants’ devices frequently handle large volumes of email that may contain phishing attempts or malware. Placing these devices on the same network segment increases the risk that a compromise on one device could spread to sensitive data on another. Creating separate VLANs for HR and administrative staff helps mitigate this risk.
In 2026, cyber threats are defined by their ability to rapidly gain initial access, pivot across network resources, and exfiltrate data while evading detection. While network compromise cannot always be fully prevented, implementing network segmentation through VLANs can slow lateral movement and give defenders more time to respond. Therefore, network segmentation remains a key requirement for a strong security posture and compliance with this framework.
